Currently, more people want to hack someone’s phone remotely than those who can actually do it. While it’s deemed not to be a simple procedure, it’s now doable. Another thing, you don’t need hard coding skills to master this art.
There are many applications out there designed to help you with hacking any phone remotely. While you are bound to get apps that pose to work but not, there are good ones out there.
If you can read instructions and follow them, then in most cases, you will get through the hacking procedure. That means being able to hack a phone and access all the data you need without it.
Here, we will talk about five of the best apps that can help you hack without the target’s knowledge. This is an answer to the question if you can spy on the phone without having it You’ll get to know them and see how they can work to your advantage.
mSpy is probably one of the easiest methods for hacking cell phones remotely. Rather than forcing you to enter their credentials, mSpy takes a smarter approach. With the app installed, just head to your mSpy account. There, you’ll see a very cool dashboard that shows you what’s happening on your phone. Just click the Social Networks section in the left panel, and you’ll immediately see their conversations, just as they appear on social networks on their phone.
You’ll find several tabs, including a chat tab that shows you all their messages, a Contacts tab that shows you, everyone, on their contact list, and a Phone tab that shows you who they called (and who called them).
Part 1: Hacking Someone’s Phone Remotely with Spyic Solution
One of the best apps that can help you hack a variety of phones is the Spyic monitoring solution. Millions of people in more than 190 countries have already used it to help them in hacking their targeted interests.
It has also gone ahead to win recognition in some of the most recognized news outlets. Some of them include Tech Radar, PC World, CNET, and Forbes. The reason behind the popularity is how it works to achieve the remote hacking process.
With Spyic, you can hack all the data you need from the target without their knowledge. Spyic operates while hidden (stealth mode), which means your target is never aware of your hacking objectives.
When it comes to the captured data, you get to see the calls, messages, social media updates, location, and more. For more information about what Spyic can do, make sure you visit the demo page via the main website.

How Spyic Works
Spyic works on both Android and iOS platforms. So, apart from the associated phones, you can also use to hack the related tablets. The best thing with using this application is that it doesn’t involve any rooting or jailbreaking.
It’s, therefore, safe to use since it doesn’t involve tricks that may alert the target user. If you want to hack an Android phone, Spyic requires you to install it once on the phone you are targeting. After that, you will not need the phone again.
One thing you need to make sure, though, is that the Android has OS version 4.0 and above.
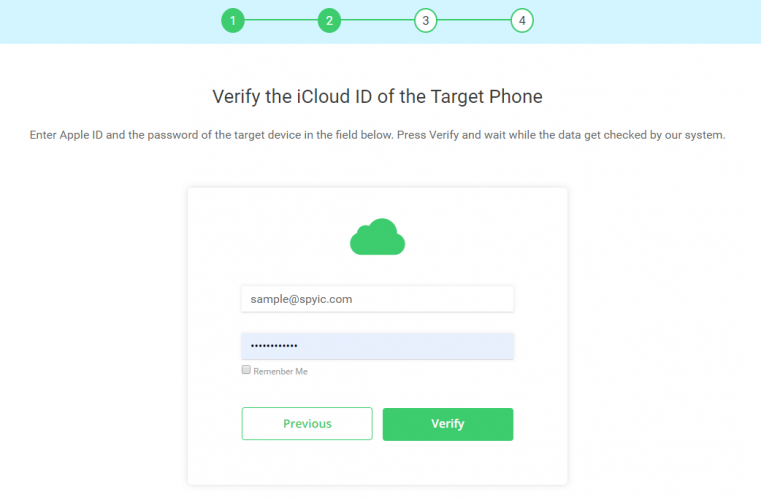
When it comes to iOS hacking, Spyic does not need any download or installation. If you have the iPhone’s/iPad’s iCloud details, that’s all you need to get started. For the Apple devices, make sure they have iOS version 7.0 and above.
Once you set it up, regardless of the phone’s OS, the results are viewed remotely. To make that possible, you will need an account with Spyic first before the setup. That is what you will use to see the fetched information.
Your account will host Spyic’s control panel that is user-friendly and web-based. It’s also compatible with all browsers so, you can use any device (from computers to smartphones) to view the results.
Now that you know what Spyic can do, here is how to hack someone’s phone without having it.
How to Hack Someone’s Phone Remotely Using Spyic Solution
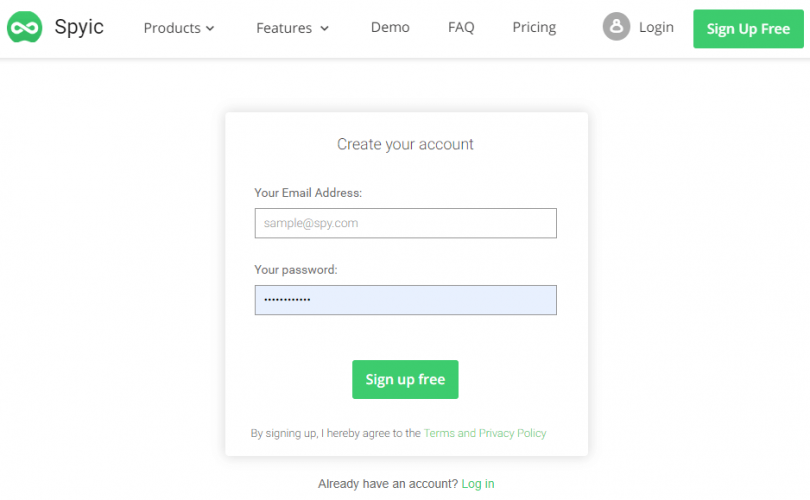
Step 1: Go to the Spyic website and register an account with your email address and a password. After that, select the targeted phone’s operating system to continue.
Step 2: You will land on a page with the pricing plans. Choose the one that fits your hacking needs and
make a purchase. You will then get a confirmation email with the login details, receipt, and the setup guidelines. For Android, you will also get a download link.
Step 3: In Android, use the sent link to download and install Spyic on the phone you want to hack. Make sure you activate hidden/stealth mode by selecting the ‘Hide Application’ option. Next, finish up the installation and get ready to access the phone remotely.
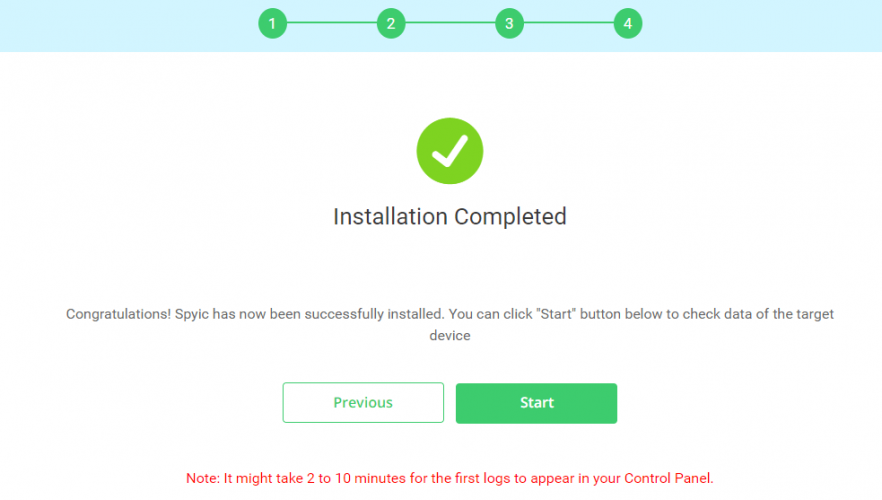
Step 5: Once you have re-accessed your account, and waited for the Spyic and Android/ICloud syncing, you will see the dashboard. It will have all the hacking features you need on the left menu. On the right, you will see the phone’s activities in summary.
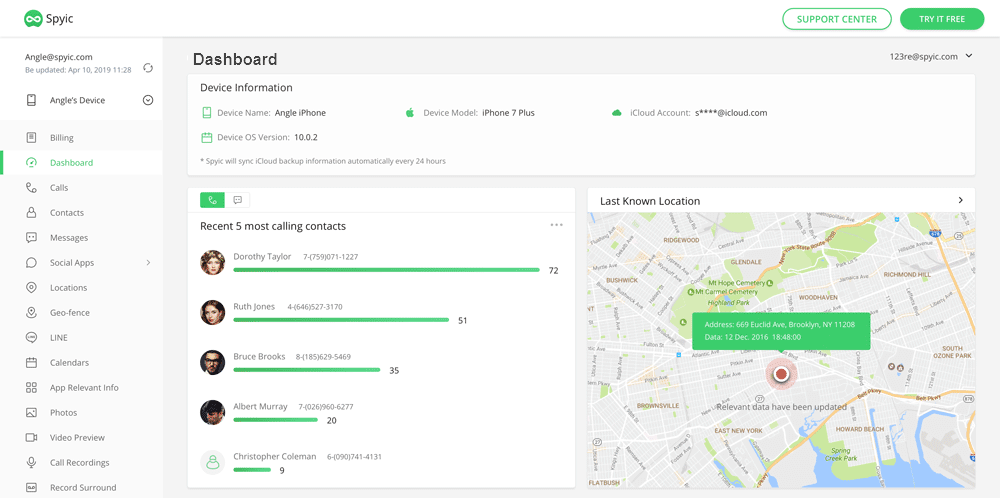
To see what Spyic has fetched remotely, click on each of the elements on the menu. See the calls, messages, location, social media updates, browsing history, etc.
Part 2: Hack Someone’s Phone Remotely with Cocospy Solution
Another reliable app that millions of users have depended on is the Cocospy monitoring solution. With Cocospy,
you can hack every bit of valuable information from the targeted phone without alerting the user.
Another advantage of going for Cocospy is that it allows you to receive the hacking results remotely. It’s an app that can reveal the calls made or received, sent and received messages, social media activities, and more. You can also use it to track the target’s location remotely.
Just like Spyic, Cocospy also works on both Android and iOS devices without root or jailbreak. It also works while hidden when fetching the data for you. Those are the specifications that make it reliable, secure, and discreet during the hacking expedition.
In Android, you need to install it once on the targeted phone before accessing it remotely. In iOS, you only need the iCloud credentials to start and continue hacking the iPhone/iPad. After setting it up, the hacking results are viewed remotely via your established account.
The account will host Cocospy’s online dashboard that works with all browsers. Whenever you need to check on the updates, you just have to log in to your Cocospy’s online portal.
For more information about Cocospy, visit the website and make sure you check on the demo page.
Part 3: AndroRAT
AndroRAT is an acronym that stands for Android RAT (Remote Administrative Tools). It’s a free hacking app that has been around for quite a long time now. During its initial release, it came in as a client/server app.

That being said, AndroRAT allows you to remotely control an Android device and fetch the information you need. When using it, it will run as a service after the booting process. That means there is minimal interaction when kick-starting it.
When hacking, you can trigger the process by creating a server connection via an SMS or call. After the server contact, you can make use of features that will fetch you data from the targeted Android.
They include getting the call log, location, contacts, and messages among other details. It can also allow you to monitor
the Android state, make remote phone calls, send messages remotely, etc.
You can also use it to take a picture remotely or open up a URL in the device’s default browser.
Part 4: NordVPN
NordVPN is a Virtual Private Network service provider that can assist you in hacking Android and iOS phones. During the hacking task, it’s possible to land on a rooted/jailbroken device with no protection in public Wi-Fi.
That is where you need NordVPN to sniff passwords from the targeted devices.

While it seems to be a remarkable method, it also leaves you vulnerable. In public Wi-Fi, data is broadcasted in all directions, and there are data packets (and cookies) roaming in the air.
While that’s not literal, it’s possible to listen to such kind of data and access what you need. If you know an Android or iOS device in public, this is one of the ways to hack it.
What the VPN does is connect you to a remote server. After that, all the traffic is routed via that server. That is how you
get to hide your details during the hacking process.
Part 5: Shadow Spy
The last app on our list is the Shadow spy application. It works on both Android and iOS devices discreetly. That means it also hides during the hacking operation. Once you acquire it, you get to try it for the next 36 hours before making a payment.

The updates are received remotely, which implies that you don’t need the targeted phones after the installation. Some of the features that you will find reliable here include internet history, GPS location, and FB, and WhatsApp hacking.
They also provide 24/7 customer support in case of any issues.
Conclusion
If you thought that hacking phones remotely is impossible, you now have five answers to testify. Here, we are recommending Spyic above the rest. The reason behind it is that it’s secure to use, works while hidden, and you get real-time hacking updates remotely.
If you have any questions regarding this blog or any other hacking apps, or are looking for the exam visit Exam-Labs.
Don’t forget to check out our ‘What Gadget Reviewed’ store, now available with discounted tech!











This Hacker is everything, he worked for me once but i totally recommend him, he’s an expert, he did a professional job, that i can’t say, (classified) find a list of his services below, listed by priority
Credit Score Repair and Fix
CC TopUp
Cellphone Clone/Hack
Social Media Accounts Hack
e.g Facebook WhatsApp Instagram…etc
GPS Tracking (Location Tracking) and much more, you can ask him to draft a better list of his services when you are in contact with him.
pavelnovakbreach@gmail,com
I’ll forever appreciate the expertise of StealthyHacks@, gmailcom for a tremendous and stupendous service delivered when i needed to see through my cheating partner’s mobile phones.
The best phone infiltrator to contact for all mobile phone cloning and cryptocurrency recovery services is RecoveryBureauC @ Gmail c0m. Few days ago I hired him to spy my suspected cheating spouse phone to gain vivid proof of her cheating husband ate which he did. I also hired him to recover my stolen cryptocurrency assets from a fraudulent crypto investment website which he did perfectly. He’s the real deal
If you have ever lost your bitcoin wallet recovery phrase or lost your funds entirely to investment scammer you know the feeling isn’t a pleasant one,
however don’t loose hope because these guys could help you recover your wallet and funds by tracing the transaction from the blockchain network.
I contacted them when I found myself in a similar situation but was able to recover my wallet using their help, Remedyhacker1 at g,mail,c0m
It costs absolutely nothing to stay loyal in a relationship, but the modern relationship has turned out to be a thing of disloyalty, cheating and excessive manipulation. Being a victim of infidelity made me feel depressed and was mentally drained as I kept asking myself if I wasn’t good enough or wasn’t doing enough to warrant my partner to cheat in the affair. I was worried and curious about the crooked attitudes in the relationship and decided to see for myself if my instinct was right or wrong, hence why I requested the help of a an expert (Stealthyhacks@ Gmailcom) whose service granted me access into my partners phone to see who my partner has been texting and what my partner has been hiding in the secret chats, and deleted messages. It broke my heart that I was taken for a fool as I was completely cheated on, but I was glad I was able to confirm that my instinct was right about the whole situation.
Sometimes last month my spouse started
misbehaving and acting weird she’s clingy with
her mobile devices which made me develop a
suspicious mindset towards her phone activities so I became curious to know what she’s been doing on her phone lately so I searched the internet for the best and efficient phone spying expert I found RecoveryBureauC through Mspy reviews from a trusted and verified user so I decided to give this tech genius a try to know if he can truly help me in my case. Fortunately for me it was the right step and best decision. I reached out to him via his contact address at RecoveryBureauC @ g mail, cOm and told him about my situation and he promised to deliver a satisfactory service at the shortest time possible which he did. I hired him and within few hours all information from her phone and internet activities popped in and it was as if I got her phone in my palm. I got to know she’s been cheating all along our relationship with a guy downtown which got me infuriated I’ve been channeling my resources in terms of affection, time and funds wrongly. I became depressed and when I showed her all proof and evidences she couldn’t deny it. It was all like a dream to me but kudos to the tech prowess of RecoveryBureauC via gmail, cOm who rescued me and restored my life back on track and reduce my losses. If you ever found yourself in a shady relationship, RecoveryBureauC is the best to hire for phone monitoring services.
Email: RECOVERYBUREAUC @ GMAIL COM
Real deal
Hire the best phone monitoring expert to remotely spy and clone your suspected cheating spouse phone with trade by sending a detailed mail to RecoveryBureauC @ gmail c0m. He’s the best and the real deal
Before trying to check your boyfriend’s phone, I’d suggest you calm your nerves and go through this article—> https://qr.ae/pyFsBL as it helped me overcome the anxiety of knowing what my partner might have been doing behind me, it really helped as my instinct was right.
I wouldn’t have been able to hack into my partners instagram and snapchat without the help of ( HACKCOPERATION @ gm ail c om ) I had a hard time finding the right hacker who could pull it off without my husband noticing what was going on, This hacker has great reviews and I have come in contact with people who has used his service successfully and he delivered. He is the best amongst them and his services were splendid and the cost was effective. i highly recommend this hacker
Hi everyone, never worry about losing your social media account password, email password, or having your phone hacked. These hacking procedures are nothing to them with computer speciallist recovery. All you have to do is get in touch with computer speciallist Recovery, let them know you require the aforementioned hacking service, and wait for the task to be completed successfully. The brilliant and diligent minds never let you down. After two days of contacting computer speciallist Recovery, I was able to get my email password back. They are a really good hacking group now that computer speciallist Recovery is available. Make sure to send a notification through one of the platforms below for proper communication. Via email them: computerspeciallist@engineer.com
Many thanks computer speciallist .
Hire RecoveryBureauC @ Gmail c0m for all professional spying and investigatory services such as mobile phone cloning, boost of credit scores, recovery of stolen cryptocurrency etc. They are the best
Most men are in a relationship that is full of lies and deceit but they don’t know how to go about it because they don’t have any evidence. Have once been in that situation and I know how painful it is until I saw a post here referring techspywiz @gmail com. I decided to contact them and they were able to give me full access to my partners phone without leaving any traces… I m saying big thanks to this team and also referring them to anyone who might need their help as well.
Many more people want to hack someone’s phone remotely to access all the needed information. While it’s known to not to be a simple or easy procedure, it’s very very doable with real working professional skills of a pro.There are many applications out there designed to help with hacking any phone remotely. While you are bound to get apps that pose to work but not, there are good ones out there, maybe but now none that has worked for me except when i use the skills and hacking tactics of a known professional hacker( HACKHUBMAYORS @ YAHOO. COM. )
If you can read instructions and follow them, then in most cases, you will get through the hacking procedure OF THIS ETHICAL ONE and That means being able to hack a phone and access all the data you need without it being compromised or detected by any target mobile or devices.
How hard it is to find help without knowing exactly where to turn upto. being in a relationship of love and trust has always been my desire and i felt so happy after having one for myself, he was so nice at first but i needed to make sure his love confession to me was true mostly about things he said about himself, i asked ”WIZARDHARRY (@) PROGRAMMER (.) NET” to help me carry out a background record check and also help me with access to his WhatsApp, please do understand i had my reasons for this, he don’t always answer calls from a Number saved on his mobile by the name Sweet Dad when ever he is with me. After having access to his WhatsApp account I discovered his sweet Dad was his baby mama who still goes out with him always. Thanks to Harry I found out the truth I needed, honestly it hurt.
As definite as it is, there sure is many ways for one to be able to access another persons mobile devices. amazing thing is that there sure is real applications that can guarantee ones access to spy and fully attain needed information from any place necessary without challenges or detection of hacking procedure to your target. there’s no denial that what people who seek these services want is to have a hundred percent access to view all kinds of messages from all sources and many more like observing logs of calls, media accessing of sent and received, live location accessing and all tabs of many more. story short, these can be achieved when professional skills take care of such, needed by all of such in the need, in the world. yes apps work but honestly, they mostly have limitations as I’ve never used one without any and these may raise the red flags. truth is, I have seek these services and more but with only ethical skills of hacking do i get this done smoothly with no trace or detection to target, not at all. with all the credit to a well known pro for real results, attestable by many others. ( SPEEDNETTECH@AOL.COM) TRULY, again, truly does giver reliable working results. so do some real working apps i read about. so far, none for me but with real working proof of professionalism. (SPEEDNETTECH@YAHOO.COM) 100%
HIRE A HACKER/ RECOVERY EXPERT TO TRACE AND RECOVER STOLEN/SCAMMED CRYPTOCURRENCY ASSETS CONTACT RECOVERY MASTERS:
Common mistake that is countlessly repeated by most cryptocurrency traders is investing in the wrong online cryptocurrency theft platforms which usually promises them huge profit on their investment only for them to end up losing all of their investments. I was also a victim of this early this year but was able to recover 95% of of my Crypto to my Trezor Wallet with the help of trusted licensed hackers
RECOVERY MASTERS they are Very professional and friendly when dealing with Clients.I will highly recommend them incase you need such services.
contact email (Recoverymasters@email.cz or whatsapp +1(204)819-5505.
Hello everyone, I’m going to share my story of how I got myself out of a financial crisis. I met someone on Instagram who told me how I could make huge profits from investing in cryptocurrency, I fell for his scam and started investing to the point where I invested my entire savings and took a loan after he thoroughly brainwashed me into investing more to gain financial freedom. To cut the story short, I had invested $74,000 in bitcoins into this scam, I was depressed to the point of taking my life when I came across an article about a hacker Richard Pryce wizard, who was able to recover money lost through a cryptocurrency scam for several other people, I hurriedly contacted them, I don’t know how it was possible but Richard Pryce wizard was able to recover all my money in the space of 48 hours. I’m still in shock from this experience but I’m truly thankful to Richard Pryce wizard and I would love to put this out there to everyone that if you think all hope is lost then you should contact them to help you find a solution. They will recover everything you lost to these scammers in a matter of hours. Thank you so much Richard Pryce wizard Their contact information is (richardprycewizard2016@gmail.com )
Most men are in a relationship that is full of lies and deceit but they don’t know how to go about it because they don’t have any evidence. Have once been in that situation and I know how painful it is until I saw a post here referring hackerspytech at gm ail c om. I decided to contact them and they were able to give me full access to my partners phone without leaving any traces… I m saying big thanks to this team and also referring them to anyone who might need their help as well
BITCOIN RECOVERY
Hello. I’m Richmond Fischer here, thanks for reading.
For any cryptocurrency recovery requirements from a reliable recovery company, I advise WebShell. I would currently be homeless and heavily in debt if WebShell hadn’t assisted me in recovering all the money that had been fraudulently invested in bitcoin that had been taken from me.I genuinely appreciate his help and experience in making sure I receive everything back, whether I’m at home, in jail, or both. After reading their email, I protested to them about falling victim to a fictitious cryptocurrency and FX investor. In less than 48 hours, all of the money that had been taken from me using Bitcoins had been restored to me. I wholeheartedly encourage anyone who may require their assistance to contact
WebShell can be reached via Email / WhatsApp at
(Webshell@cyber-Wizard.com)
+13195191428.
Infidelity sucks
I’ve been a victim of infidelity and I can tell you vividly that it hurts, and worse if you couldn’t get an evidence to proof your sanity. Few weeks to my weeding I caught my man red handed cheating on me just with the help of hackerspytech at gm ail com After my past encounter with some hackers I thought this isn’t possible. I was able to find out right on time . Thank you so much hackerspytech at gm ail com
The day i was scammed was the same day i lost my daughter, i was totally destroyed emotionally for 3 month. i didn’t have a dime left in my bank besides my credit. all my life savings was cleared from my bank by some investment scammers which i shared my banking details with. the police and the bank only filed a report and closed the case, i was left all alone to suffer it and i can swear it was a living nightmare. Not until my in-law introduced me to his old college mate who is now a hacker, he lives in united state and is very dedicated to his recovery work. it took him only 2 days to recover everything through a system he called “wizard asset-finder recovery”. i know very little about what he did but i got everything back. it feels so so miraculous to find a patrick. i would drop his contacts below just because i am over joyous, kindly message him and help me thank him more for saving my life from the pit of hell. patrickbenardwizard@gmail.com and Whatsapp : +1(908)718-7855
they provide recovery services in binary options, forex international financial fraud and more. they also engage in account management and other trading activities like bitcoin investment and exchange. they recently recovered the sum of $75,000 for me and i am very greatful to Mr Jeanson James Ancheta wizard who linked me up. using the most advance investigative techniques, this group has also recovered millions of dollars for victims of fraud around the globe. you can contact me on email:jeansonjamesanchetawizard62@gmail.com or Telegrem Number:+31684518136 so i can introduce you to them if you are also a victim
Get into your spouses and kids phones and other gadgets without them knowing or suspecting. It feels good anwd safe to know what your family members and loved one’s does at always without them knowing . I had always thought it was never possible to monitor your partner or children without them noticing, but all thanks to him I am able to view my partners activities without her even knowing
Write to :
spyhackersw AT Gmail com
Do you need a hacker? Do you need to access your partner’s email to keep track of him? As a parent, would you like to know what your kids are doing on social media everyday college grades change, (including Facebook, Twitter, Instagram, WhatsApp, WeChat and other things to make sure you don’t have problems? Banking, Cash Flow, Criminal dossier, DMV) Tax, call him and he’ll do the job. He is a professional hacker with years of experience. Write to him through [hachrighttech@gmail.com].
It actually turned out that I had trusted the wrong people/platform to manage my trades and stock , I never imagined I’d ever be in a situation whereby I’d be scammed of my money and all , this set of people were very nice and compelling right before I got involved with their company , I could recall one of my friends telling me about all this online investment company that come right to your DM to offer you a n enormous deal of money after investing with them , sometimes I blame myself for not listening to her at first, I will say that I was so desperate to earn a good living and ended up in the wrong hands , but later in I still regained back what was rightfully mine with the help of VIRTUALHACKNET AT gmail dot com . I can assure you that nobody does it better than this very same team I worked with . Make sure to contact them and I bet you’d never regret working with them . Very active on telegram @VIRTUALHACKNET .
No matter how good you are to them it doesn’t mean that they will treat you the same way. I have been married to my husband for years with no idea he was cheating. Suddenly i started noticing changes in behavior, i suspected something was wrong. So i was rescued by digitalhackelite at gm ail c om, he was able to help me with solid cheat proof by getting into her phone to retrieve text messages, call logs and lots more. If you feel you have same issues you can reach out to him. I’ve tried this app, it help.. Extraordinarily phenomenal Help…
It costs absolute nothing to stay loyal in relationship, but the modern relationship has turned out to be a thing of disloyalty, cheating and excessive manipulation. Being a victim of infidelity made me feel depressed and was mentally drained as I kept asking myself if I wasn’t good enough or wasn’t doing enough to warrant my partner to cheat in the affair. I was worried and curious about the crooked attitudes in the relationship and decided to see for myself if my instinct was right or wrong, hence why I requested the help of the genius mind techie; Stealthyhacks@ Gmailcom, whose service granted me access into my partners phone to see who my partner has been texting and what my partner has been hiding in the secret chats, and deleted messages. It broke my heart that I was taken for a fool as i was completely cheated on, but I was glad I was able to confirm that my instinct was right about the whole situation.
This review is solely based upon the originality of monitoring apps, it’s quite obvious there are many fake and dubious apps and reviews that are under the guise of being the real deal. I must say to you today that the best way how to see who your partner is texting is by using dedicated monitoring apps created by people like VoltronHackers @ G. Mail com, these apps make it easy to track incoming and outgoing texts on your partner’s phone without them ever knowing you’re doing so.
These apps are designed to be completely undetectable, meaning that even if someone checks their phone for suspicious activity, they won’t be able to spot the monitoring app running in the background. One of the benefits you would love is that the monitoring app allows you to view your partner’s text messages on all kinds of social networks, isn’t that cool?
We all have our separate reasons for hiring a hacker. I was faced with such a problem sometime ago and I didn’t know where to look for one, so I went online and searched. And a lot of results came up during my search but I choose hackerspytech at gm ail c om and after talking with him and relaying what I wanted him to do for me, he told me not to worry he collected some information from me and told me he’ll get back to me within 6 to 8 hours so after waiting for about 6 hours he mailed me and said my job was ready. he gave me all the proof and evidence that my husband was cheating on me with a neighbor for 3 years now. And with that I was able to confront him. contact him for any hack problems and get the solution to your problems fast! Text him on hackerspytech at gm ail c om
Most men are in a relationship that is full of lies and deceit but they don’t know how to go about it because they don’t have any evidence. Have once been in that situation and I know how painful it is until I saw a post here referring spyhackersw AT Gmail com. I decided to contact them and they were able to give me full access to my partners phone without leaving any traces… I m saying big thanks to this team and also referring them to anyone who might need their help as well.
If you’ve ever thought your partner was cheating on you – even when they weren’t – you’re not alone. It can be a very stressful situation to find yourself in. And while it may seem like trust issues are what’s leading you to constantly worry your partner is cheating, experts and research say it could point to something deeper than that. It’s a slippery slope, but the good thing is you can overcome it. I found myself in those shoes and could not get myself enough peace until I sought out a professional-hands on, I contact spyhackersw AT Gmail com to help access my spouse device so I can get proof. Well it turned out it wasn’t just thoughts, I was being cheated on. I got complete access to my spouse device from mine, messages calls chats everything. You can contact them to clear your mind from worry.
I’d recommend that y’all reach out to digitalhackelite @gm ail c om for a quality social media hack service. Their services are great and top notched
This hacker sounded and was very professional in providing the texts and features that were required from my spouse other device His customer service on Whatsapp were polite and readily available to provide the features. such as whatsapp, Facebook, text messages, call logs Reach out to digitalhackelite @gm ail comn on google mail. Highly recommended
I’ve been struggling with how to hack someones WhatsApp messages without touching their cell phone for almost a year. I’ve tried at least 10 different apps and none of them worked. I found smarthackersw AT gmail com after reading a blog post on how to hack someones WhatsApp messages without touching their cell phone and the reviews were all good so I thought I would give it a try
This hacker sounded and was very professional in providing the texts and features that were required from my spouse other device His customer service on Whatsapp were polite and readily available to provide the features. such as whatsapp, Facebook, text messages, call logs Reach out to spyhackpro9 @gm ail comn on google mail. Highly recommended
It’s been pathetic losing your hard earned money to crypto investment theft scheme which are currently on the rampage over the past few months. With the recent crash in FTX platform, I lost all my savings and could barely have my three square meal. I was in disarray until I looked up hackerspytech {at}gmai| c 0 m who assisted me and got back my stolen funds completely. This got me back on track and happy to celebrate the festive season with family and friends
Most men are in a relationship that is full of lies and deceit but they don’t know how to go about it because they don’t have any evidence. Have once been in that situation and I know how painful it is until I saw a post here referring techspywiz @gmail com. I decided to contact them and they were able to give me full access to my partners phone without leaving any traces… I m saying big thanks to this team and also referring them to anyone who might need their help as well.
I am a victim of the renowned legacyfxglobalmarkets scam which all started with just a deposit of £400. The next deposit I was forced to pay quickly turned to £1,500 and every time I tried to cash out they asked for more to cover for UK taxes and other complicated government fees. My profits had accumulated to £117,000 as it would show on my mobile application but I could not access it. By the time I came to my senses that the company is illegitimate, l had already lost a total of £50,000. I researched about the company to confirm my fears and I came across a page where other people who had lost money to them shared their stories. Among the comments was from an elderly guy who shared how he got his profits back through the help of GearHead engineers. I decided to try my luck and presented my case to them, which they were already familiar with and so I got back everything within 24 hours. I’m writing to confirm that Gearhead is absolutely functional. Go to their website gearheadengineers.org and chat with them from their chat feature to avoid impersonators.
Most men are in a relationship that is full of lies and deceit but they don’t know how to go about it because they don’t have any evidence. Have once been in that situation and I know how painful it is until I saw a post here referring techspywiz @gmail com. I decided to contact them and they were able to give me full access to my partners phone without leaving any traces… I m saying big thanks to this team and also referring them to anyone who might need their help as well.
Try Using spyhackpro9 @ gm ail c om ,although they are slightly expensive but they know exactly what they are doing. Always make research before hiring a hacker and never hire a hacker with gmail account. They are all scam. You can use “spyhackpro9 @ gm ail c om ” and you can be able to have some questions for them.
I highly recommend anyone who has lost money through fraudulent means the services of Software Specialist. He is professional, trustworthy and honest too. He also offers services such as: phone and computer hacking, social media account hacking, changing school grades and email hacking. I came into contact with Software Specialist (softwarespecialist@usa.com) when I became a victim of crypto scam and I was looking for a way on how I could recover back my investment. He helped me recover my lost 38,000 USD I invested with a company in China. The company ended up compounding my funds and when I requested for a withdrawal, it was always declined. Days later, the company shut down their website and that was when I realized I have been scammed. That was when I quickly reached out to Software Specialist who I owe a lot because it is so hard to see legit help online.
The best professional tech personnel to hire for all mobile phone cloning and recovery of stolen cryptocurrency assets is RecoveryBureauC @ Gmail c0m. This expert was able to rescue me last month from a pig butchering theft scheme which I got lured to and I lost almost 345,000 USD but after days of depression I met RecoveryBureauC and he recovered my funds completely without hassle or hidden fees.
I employed him two days ago to spy and monitor my suspected cheating husband’s phone and he delivered. He’s the real deal
Incase you are one of the people looking for means to recover their stolen funds, then I know the best team to help you recover your stolen money or investment of any such, I was once a victim of scam and after so many months, I was able to recover my lost funds through the help and services of COREASSETINC @ GMAIL.COM if you by chance come across this review , I am writing this out of experience, i recovered my lost investment with the team I mentioned above and their result was perfect after seeing all my Lost investment reversed back into my trust wallet , It was really unbelievable to me at first but it’s reality. Can’t really thank COREASSETINC enough for helping me when I was helpless ..
All thanks to the humble and expert hacker at COREASSETINC @ GMAIL .COM , Last 3 months I contacted the company for a job , after I read several reviews about them . I even reached out to one of their clients who had worked with them in the past just to verify how genuine they are before I could proceed with the work at hand with them , they were able to retrieve back my 600k worth of BTC that was stolen from my wallet when my email and computer was attacked and my wallet phrase was there as well when I tried working investing with a Russian based investment company , not knowing they were fake and never existed , he got the job done within 3 weeks after I contacted their team … here is their contact address
Email : COREASSETINC @ GMAIL . COM
In my pursuit for solutions to get back my funds, I contacted the JETHACKS RECOVERY CENTRE INC. after reading so many positive reviews about the Team , naturally am a risk taker but my friends !? I can’t say the same so when I first told them they weren’t buying it .. just being extra cautious after the whole situation that’s been going on with the company but that wasn’t going to stop me .. I was willing to do anything so I contacted the JETHACKS CENTRE INC using the contact details I found online
EMAIL: JETHACKS7 @ GMAIL .COM
TELEGRAM : JETHACKSS
My funds have been trapped in a foreign crypto investment company , I wrote to them on Email and the rest became history . Now my friends believe in me they’ve seen the achievements and the excellent work of JETHACKS RECOVERY CENTRE INC. and how he restored the funds we almost thought we lost , they have reached out to The Team and had their funds recovered as well .. you can recover your funds as well , just reach out to the JETHACKS RECOVERY CENTRE INC. on any of the above contact .
I noticed that my wallet has been compromised after I noticed a withdrawal of $700k worth of bitcoin was made and was not made by me , I was so curious to know what happened and retrieve my bitcoin back ,it happened that my wallet phrase was stolen but still can’t explain how it all happened so quick .. I quickly reached out to one of my colleague at work who also invests in crypto currency , he then gave me a contact who helped him back then when he was in the same situation as me , I reached out to COREASSETINC@ GMAIL .COM , and after explaining everything to him , he assured me he was going to retrieve it all back and he kept to his words , within a space of 1 weeks he pulled it off , I never thought this was even possible at first but with COREASSETINC @ GMAIL .COM I believe nothing hack related is impossible .
Best Crypto Recovery’s Experts/George Wizard Recovery Home My experience of online scamming took seconds and cost me thousands. I was fooled by a YouTube video that convinced me that I could make a killing in Crypto, and the minute I clicked the link and deposited funds, I knew something was up, but it was too late. I worked with George Wizard Recovery Home, and they were so helpful and supportive, and in the end, it took a 24hrs , I got almost all of the money back. It wouldn’t have been possible for me to meet up economically because I almost invested all my money but all thanks to George Wizard Recovery Home with their genius effort to help me recover my already stolen currency. Please ensure also to consult if you need such help:via email: (georgewizardrecoveryhome@gmail.com)
(info@georgewizardrecoveryhome.com) or whatsapp (+1 (908) 768-4663)
Anyone could be a victim of this or any other scam. I went through the worst period of my life after getting wiped out b a scammer and only thankful for the intervention i got after i filed a complaint via email to – support (@) (digitalprohackz) @ gm ail com
my name is Angela Scott from USA
Get Advice From A Certified Bitcoin Recovery Specialist /CYBER WIZZARD
The CYBER WIZZARD is a global licensed forensic organization that can help you recover stolen bitcoin or tokens.
Ultimate CYBER WIZZARD specializes in recovering bitcoin and tokens that have been taken from you by crooks.
To make sure that no one can move your money without your consent, the cryptographic protocol guy used a decentralized recovery system to track the wallet balance using smart contract audit from the outsourced wallets on
( cyberwizzard@seznam.cz)
Whatsapp (+33752749058)
extensive database built on blockchain technology.
In the year 2023 we investors need to be careful, despite my experience, tried to always be careful when it comes to investment or trading Bitcoin, but this swindlers or scam have fake site, I was a victim of scam early this year and I lost over half a million dollar worth of Bitcoin, yes there are lots of scams out there and most of us tends to be the victim of this scams, I had already lost a huge amount of my bitcoin investment in march 2022 with an online investor, i gave access to my wallet and they got into my account as well, and cleared it all, in September during yoga I met with Catherine and shared the problem with her then she referred me to Coreassetinc a recovery firm who’s an expert in tracking and recovery of bitcoin , at first I didn’t give in until I had read lots of review about them, then I realize how possible it is to get back your wallet, so I followed some legal procedures with the company, I started by sending an email to COREASSETINC@ GMAIL.COM and afterward I got a response and when I shared proof and documentation they assured me and went on to retrieve back my wallet and the fund….. I thought it was a scam when I started with them but it all turned out to be legit… there’re still some good company of people out there with integrity, if you find this helpful you can start by sending a request mail to the contact provided above. I hope this is helpful to someone out there.
Please be wary of the many scam investment websites everywhere , i got scammed by a well articulated investment website . The whole plan they sell to you will sound so smooth and straightforward there will be no room for you to doubt it. I came to understand that cryptocurrency mining/ investment is a good one if you are in touch with the right investment team. I invested a lot which was in a series of payments in one of these websites. Crazy thing is that i monitored the profit and it was looking really transparent as I had a dashboard to monitor my investment but i got locked when i was about to withdraw and this gave room to more payments which they claim we’re taxes and were going to be added to what i will be receiving. I went searching online for a solution because they hit deep into my savings and i eventually met this team of experts that i got in touch via mail to help me handle recovery of my money. COREASSETINC @ GMAIL.COM I sent a mail to them and was able to get about 100% of what i lost in less than 3 weeks.
Thanks Jessica, i had been suspecting my spouse for sometimes, i saw your reviews few weeks ago and i decided to contact him which right now is the best decision i have made in my life. I got access to his phone and saw some hidden things he is been doing around. I’m happy to took the right decision cos i got access to everything ranging from call records, text messages, social media activities account on the phone plus Gmail. He is so good and i can vouch for him. You can reach him today via..
Email:[hachrighttech @gmail com].
I thought I was entering an age of new money from online investment when I learnt about binary options, I was greatly eager to get on board even more especially because i had some knowledge of online trading, everything changed when I was ready to make my withdrawal and I could get nothing. The entire thing literally broke down in my face when I became convinced my money was stuck with them, read came across a recovery experts and they did a good job helping me settle a problem that was having me sick daily, they recovered every thing I invested . I’m quite impressed by their work, you can contact them ;
Email : COREASSETINC @ GMAIL DOT COM, Telegram : @COREASSETINC .
Hacking a mobile phone is usually something that requires hiring an expert to get it done for you to get your desired result. These mobile hacks actually work fine but most people have problems using it because bulk of the job is done and highly dependent on the hacker. In most cases, the only way you can get it done yourself is if you really know how to hack. Otherwise, your best bet will be to hire a professional hacker, and I recommend [hachrighttech @gmail com] I have used the service and his is highly professional, he’s the best and he will give you exactly what you want.
I lost all my money after falling victim to a cryptocurrency investment scam, I was logged out of my account and was told the account manager was sick and that I had to pay some certain amount to gain access to my accounts. I had invested some huge amounts of money into this platform Capital Express FX, a lady contacted me to invest in this platform so that I would make huge profits which I did but to my surprise, these were all scams and they have defrauded several others of their money through cryptocurrency. I was weak and broke, I couldn’t meet up with my bills until a friend of mine told me about Coreassetinc, a reputable and reliable recovery company. I contacted Coreassetinc and provided all the information to them, a few other things I couldn’t provide but this company did an amazing job to trace and recover my stolen money. I’m still amazed and excited that a company like Coreassetinc is out there helping victims of cryptocurrency scams recover their money. I’m truly grateful to their service and recommend them to everyone… here is their contact address
Telegram: @COREASSETINC
Email: COREASSETINC @ GMAIL . COM
Oh my goodness .. what could I have done without VI RT UAL HA CK NET @ G MA IL dot COM “ who came to my aid when I needed it the most , I have been a real estate investor for over 5 years now , I then decided to try out crypto though I’ve heard so many sad stories about crypto companies ,tho there’s the good part and the bad part of it , but after my whole research it seemed like the bad outweighs the good . I then decided to hold crypto in my wallet , instead of investing with any platform , but that didn’t turn out well as I expected too . Along the line my brother advised that I should mine my coin instead of investing with an investment platform , that way I can actually earn much more profits than keeping it without it appreciating . I took up his advice and ended up in a ditch , I lost nearly $450k within the space of 3 months . I then reached out to @ Virtualhacknet on telegram for help after seeing people commend him for the great help he offers . Out of the whole money he was able to get back $390k which went a long way for me , I’m so excited with the outcome .
Hello everyone, my name is Cynthia Murk and I’m going to share with you all how I got scammed after falling victim to a cryptocurrency investment scam, I was introduced to this cryptocurrency scam by a guy I met on Instagram and after investing all my life savings, they swindled me off $960,000. It was the saddest moment of my life because I couldn’t believe what had happened, I was bankrupt and my credit was damaged. I reported to the authorities and there was nothing they could do to get these scammers or return my money. I thought all hope was lost and was going into depression until I came across an article online about a hacker who could help me recover my funds, at first I thought it was impossible to do that but I realize I had no other choice but to give it a try, to my surprise MICHAEL CALCE WIZARD HACKING GROUP was able to recover all my funds and upgrade my credit score, I wanted to put this out there for anyone who might be going through the same situation and have been swindled by this scammers, you can contact MICHAEL CALCE WIZARD HACKING GROUP to help you recover your stolen funds. Contact them at [hachrighttech @gmail com].
I lost about $50,000 to 2 fake binary option website as well but I am sharing my experience here so as to enlighten and educate everyone that is losing money or has lost money to a scam including binary options, dating scams, fake crypto investing scheme or platform, real-estate scams, Mortgage and fake ICOs. However , I have been able to recover my money I lost to the scammers with the help of a recovery professional and I am pleased to inform you that there is hope for everyone that has lost money to scam. here is their address
Email: COREASSETINC @ GMAIL .COM
Telegram: @COREASSETINC
Look he’s real I have confirmed it, contact (hachrighttech @gmail com) for your hack issues ranging from bank hacks, University Grades change, Email and phone hack for text, whatsapp imessages, call logs,Gps tracking and lots more. He provides proof and he’s affordable trust me he’s real. His name is Williams computer Engineer for fast respones
There is a team of reliable and
competent hackers ready at any given
time to carry out any given job
Erase criminal records
Hacking of school data base
Hack any Email account
Hack and improve your credit card
Social Media Accounts: Instragram,
Facebook, Twitter, Whatsapp etc
contact techwizard64@gmail.com
I lost about $50,000 to 2 fake binary option website as well but I am sharing my experience here so as to enlighten and educate everyone that is losing money or has lost money to a scam including binary options, dating scams, fake crypto investing scheme or platform, real-estate scams, Mortgage and fake ICOs. However , I have been able to recover my money I lost to the scammers with the help of a recovery professional and I am pleased to inform you that there is hope for everyone that has lost money to scam.
Email: COREASSETINC @ GMAIL .COM
Telegram: @COREASSETINC
After facing the frustrating challenge of trying to recover $228k worth of stolen cryptocurrency from my USDT wallet, I was convinced that it was an insurmountable task. However, everything changed when I stumbled upon an article on thedailychargeback.com. Following their guidance, I diligently submitted all the necessary documents to Alister Recovery. To my immense relief, they miraculously managed to recover $205k of my lost funds. If you find yourself grappling with similar issues of lost or stolen cryptocurrency, I wholeheartedly suggest contacting Alister Recovery at Alisterrecovery at gmail dotcom
I would love to introduce yall to
TechWiz,he has been of help to me
in different ocassions.Techwiz helped
me hack into my wifes facebook and he
also offers any hacking services and guess
what he replies instantly and charges a
good price. send them a mail techwizard64@gmail.com
A lot has been said about Binary/Crypto Investment, personally i do believe that there are legit companies out there that you can invest with as well as fake and fraudulent companies too. i had fell a victim to this fake company brokers that claim to be investors, the whole thing was like a movie to me. i had trusted them and invested a lot of money without being aware this was all scam. i can read my total investment from my dashboard but when its time for me to take my returns i was unable to do that successfully and they asked that i pay for some fees so i could be able to withdraw but i did and still could not have the withdrawal done, i couldn’t believe things like this exist until it happened to me. However.. when it results that i cannot withdraw my money i started looking for a way to recover my money back, Luckily enough i came across a forum talking about crypto recovery and positive reviews about COREASSETINC hacking service with a lot of recommendations, he was such a savior to me, he was able to access the fake company website i made my investments to and helped me recover my funds back. for some moment i got really emotional for this man services, he was so accurate and he’s very reliable, i can’t thank him enough for what he has done for me . You can contact him on email COREASSETINC @ GMAIL DOT COM / Telegram @COREASSETINC if you need his assistance on crypto recovery.
Everyone should be careful where they invest their money. Cryptocurrency has made many rich and at the same time made so many broke and desperate. In the process of looking out for a solution to get back my stolen Cryptocurrency, I got connected to COREASSETINC through a friend who knows more about him. He gave me his contact details and I got in touch with him. Immediately I had lost my 950k worth of ETH/BTC to a fraudulent investment platform. I am writing this testimony to advise anyone who has had a similar issues to open a case with COREASSETINC@GMAIL.COM , It seemed like a magic to me first but no it’s real because I witnessed it and can’t say much any further but thanks to COREASSETINC .
Hacked or Scammed Funds Recovery Expert Ultimate Hacker Jerry.
Anyone who has fallen victim to Any recent fraudulent Crypto investment schemes should reach out to Ultimate Hacker Jerry for Recovery Services. I was a victim of one of them, and I was humiliated by how I lost €114,000 to a fake Facebook investor boasting about his huge profits from the Investment scheme he was luring me to. Ultimate Hacker Jerry is a legally licensed Cryptocurrency Recovery expert who, I must say, was a Godsend. All of my funds were recovered by the special certified expert. The Expert’s responses are timely and straightforward, and I strongly recommend them to any victim who has lost Funds and needs them recovered.
Website;https://ultimateshackjerry.com/
Mail;Ultimatehackerjerry@seznam. cz)
All thanks to the humble and expert hacker that i know at Wizardwithneyblockchairhackser(@)gmail(.)com , Last 3 months I contacted the company for a job , after I read several reviews about them . I even reached out to one of their clients who had worked with them in the past just to verify how genuine they are before I could proceed with the work at hand with them , they were able to retrieve back my 900k worth of BTC that was stolen from my wallet when my email and computer was attacked and my wallet phrase was there as well when I invested with a Russian based investment company , not knowing they were fake and never existed , Wizard Withney got the job done within 3 days after I contacted their team.
I have a strong belief that this information could be immensely helpful to someone out there, as someone else might currently find themselves in the same predicament I was in a few months ago. During that time, I unfortunately fell victim to a scam involving an online trading company, resulting in the loss of both my savings and profits. Despite my efforts to resolve the issue with the company, it seemed as if I was only compounding my mistakes, as I had to pay additional fees that they demanded while still being unable to withdraw my investment. Recently, I stumbled upon this webpage, though I initially didn’t take it seriously due to the conflicting comments I encountered, making it difficult to discern the genuine from the fake .However, I eventually gather the bravery to reach out to a Wizard named COREASSETINC. I send an email to COREASSETINC @ GMAIL .COM seeking assistance, and they successfully help me. I am extremely thankful to this amazing team, who, with their extensive expertise, manage to recover all of my lost funds when I believed I had lost everything. I am grateful for their help. If anyone else finds themselves in a similar situation, I strongly recommend contacting COREASSETINC. They can also be reached on Telegram with the username COREASSETINC .
As a project manager, I had tried to invest using a platform , a cryptocurrency platform founded by the influential . The platform was plagued by technical problems, and I found myself unable to make swaps after depositing funds. I got error message after error message. I kept reporting the issue, and customer service representatives told me a solution was in the works. Then in April of 2022, announced that the platform would be shutting down all operations that June. I did as the platform advised and immediately started trying to withdraw my funds. But I would never see that money again. I just kept getting errors trying to get my tokens out, At first, the platform’s representatives were responsive, assuring me that they just needed a few more days. But months went by. The platform stopped responding to my pleas, and the platform ultimately shuttered. All told, I lost about $162,000. Around December I got to see a wizard expertise whom I got on telegram (@COREASSETINC) they asked me some really necessary questions I gave out some because I still couldn’t trust the process , I got an Email from COREASSETINC @ GMAIL dot COM whom asked for my wallet I replied for some reasons it never made sense to me but I got my money back from the scammers in full I must say it still unbelievable .
I joined channels and associated web applications that are manipulating users into joining The fraud operation appears to be promoting a USDT (also known as Tether) cryptocurrency investment scheme. USDT, which is pegged to the US Dollar and known as a stablecoin, has itself been heavily criticised over its opaque practices, and has been the subject of multiple regulatory and legal probes. long story cut short I got entangled I paid 37,000k pounds even when I try to withdraw they pinned it to taxes I knew all this and how they operate after I contacted a group of expertises COREASSETINC whom helped recover my money I lost I know a lot of people will be. Victim of this crypto scam…COREASSETINC @ gmail dot com will explain how this scammers work and give you bright knowledge I can really remember I met them on telegram @COREASSETINC if I can remember vividly.. Good day
I am extremely thankful to this amazing team, who, with their extensive expertise, manage to recover all of my lost funds when I believed I had lost everything. I am grateful for their help.
. Along the line my brother advised that I should mine my coin instead of investing with an investment platform , that way I can actually earn much more profits than keeping it without it appreciating .
My misplaced cash of roughly $180k were found and recovered. I had my trading money unloaded by a broker who for three months refused to give me access to my trading account, and I had no idea that I would be able to recover it. That I could get my money back without any hassle makes me quite happy. Elite Wizard Bitcoin Recovery, who earned a reputation as a licensed binary options recovery specialist, is a technician I would really like to thank. Your broker manager is recommending that you make further deposits before making a withdrawal if you have money in your account that you intend to take out. Please get in touch with Elite Wizard Bitcoin Recovery using the information below if you are unsure how to proceed. In a matter of days, they will demonstrate to you the guild lines to recover your stolen funds.
Email: eliterecovery247@cyber-wizard.com
Phone: +1 (740) 688-0116
I almost gave up on getting a genuine and real hacker because I’ve been ripped off $755 by scammers before I was introduced to Fred Hacker that helped me build a software that I use to monitor my wife’s Facebook messenger, whatsapp and SMS, videos and location information. I’m super excited about the fact that I caught my ex by reading all his messages and even saw her sending nudes to men. So if you need his service as well contact him on digitalghosthacker AT g mail.com
I had my grades changed yesterday after payment was made
I came to let everyone know and to say thanks to y’all for the recommendation As a satisfied costumer I recommend DIGITAL GHOST HACKER to anyone in need of a hacker
Reach them on digitalghosthacker AT g mail.com
Should you spy on your partner’s phone? NO it’s not, but some circumstances might warrant that you need to, is your partner cheating? Is your spouse having extra marital affairs? We tend to ponder on these thoughts and the only way to know for sure if our partner’s are cheating is by having access to the secrets on their phones, how do we get the access? I got mine when I stumbled on this → https://qr.ae/pyFsBL , and I can forever be thankful for the answer.
I was completely taken in by a binary company, and soon they had all my deposits and profits.
I later found out that I couldnt withdraw my funds. I contacted my account manager but nothing was done.
I tried so many different ways but no luck, I almost gave up until (recoverfunds.investigator247 @ gmail.com)
completely took control and recovered all my money.
I’m excited to write about REMOTE GHOST AHCKER, he is a great and brilliant hacker who penetrated my spouse’s phone without a physical installation app. I was able to keep
Yes, it is possible for a hacker to fix your credit report. I am saying this from my experience with this genius Vladimir Smirnov. This man literally saved me when he helped me remove adverse reports and within a week my credit score had moved from the low 400s to over 780 across all the bureaus. IF YOU NEED HELP, HERE YOU GO. EMAIL: VLADIMIRHACKWORLD @ GMAIL. COM
Some of his many other services include: ERASING CRIMINAL/COURT RECORDS, Phone hacks (WhatsApp, Facebook, Snapchat, IG, Tapping & recording of phone calls…), and many other services.
My misplaced cash of roughly $180k were found and recovered. I had my trading money unloaded by a broker who for three months refused to give me access to my trading account, and I had no idea that I would be able to recover it. That I could get my money back without any hassle makes me quite happy. Elite Wizard Bitcoin Recovery, who earned a reputation as a licensed binary options recovery specialist, is a technician I would really like to thank. Your broker manager is recommending that you make further deposits before making a withdrawal if you have money in your account that you intend to take out. Please get in touch with Elite Wizard Bitcoin Recovery using the information below if you are unsure how to proceed. In a matter of days, they will demonstrate to you the guild lines to recover your stolen funds.
Email: vladimirhackworld@gmail.com
I took my time to write about him, because many have been mislead. As I came across this real hacker ‘remoteghosthacker AT gm ail c om’ I have to recommend him to you all out there looking for a genuine hacker. Thank you
amazing thing is that there sure is real applications that can guarantee ones access to spy and fully attain needed information from any place necessary without challenges or detection of hacking procedure to your target.
I was depressed for months as my wife and and 5year old child left me to go live with his mum cos I used all our savings to invest in crypto investment company, took a loan and sold my car too in a bid to pay the withdrawal fees I was desperate very desperate and I nearly lost everything but thanks to DARKRECOVERYHACKS Recovery Firm , They recovered my £867k from those heartless scammers .. it’s a long story but at the end I was happy , I am forever grateful to them.. This has made me to cross paths with them through a review on here and am writing this review here in hope that it will help someone out there , if you’ve been in a similar situation please reach out to DARKRECOVERYHACKS, they are very competent and reliable Firm . The contact details are as follow , email: DARKRECOVERYHACKS @ G MAIL .COM AND Telegram: @ DARKRECOVERYHACKS .
I consulted ethical hacker when I was involved in a bitcoin trading scam. It was unknown to me that there were systematic ways to retrieve scammed funds.
I came across a business website who promised a huge return on investment. I was so convinced. The website was good and after all the convincing, I ended up depositing 150,000 USD, unfortunately, I fell into the wrong hands.
I was really devastated until I sent an email to an expert who came highly recommended – ethicalh963 @gmail com
I gave him all the information about the events, and within a few working days, they restored 85% of my BTC back to my wallet. I was shocked and glad at the same time. With trustworthy people like Spyhackelite, I can 100% guarantee your money will be recovered back.
Hire a Professional hacker to change your grade(s) no matter the numbers, distance is not a barrier. Don’t give your jobs to amateur or hackers wannabe HOW TO HIRE write to them on: (ethicalh963 @gmail com) & Wait for their fast response and tell you what’s next. it is as easy as that, they handle the rest.Stay safe
This professional hacker Albert Vadim helped me gain access to an entire cellphone. I could see all text messages, emails, whatssapp and snapchat messages from my laptop. There was also an option where I could record and listen to phone calls. If you need help, feel free to contact Albert on his Email: Vadimwebhack@ gmail. com
He has helped a couple of my friends erase some bad records online, fix their credit report and boost their scores over 780. The man is a genius. Honestly, I never imagined someone was capable of all these.
Are you contemplating hiring a hacker to access your phone, Facebook account, Instagram account, Yahoo account, or WhatsApp, get your social network account verified, acquire more followers by any number, and perform bank wire and bank transfer transactions? Reach out to CyberPunk Programmers through email cyberpunk @ programmer . net. They have very good experience with the aforementioned problems.
Once the veil of dishonesty is lifted, individuals have the opportunity to regain their peace of mind and take decisive action. Hi Tech Recovery ( hitechrecovery21@proton.me )ensures that their clients are armed with undeniable evidence, offering them the ability to confront their cheating partners with collected information. Armed with concrete proof, individuals can make informed choices about the future of their relationships, bringing closure and healing to their wounded hearts. Infidelity remains an undeniable threat to the sanctity of relationships, leaving countless individuals in anguish. Hi Tech Recovery’s innovative approach offers a lifeline, unveiling the truth and restoring balance to relationships teetering on the edge. As the popularity of their services continues to grow, it is crucial to emphasize the importance of ethical considerations while benefiting from the valuable insights these technologies offer. Hi Tech Recovery stands as a testament to the power of truth and the strength it grants to those who dare to uncover it.
Contact: hitechrecovery21@proton.me
Telegram: @hitechrecovery
I am more than grateful to this pro hacker by the name Viktor. This man helped me recover all my social media accounts after I got hacked by some amateur. I was frustrated until a friend of mine whom Viktor had helped hack an iPhone gave me his contact. If you need help, I strongly suggest you contact Viktor via EMAIL: Viktorhackworld @ gmail. com
This genius offers so many other services I can’t mention here.
I consulted Hackerone975 when I was involved in a bitcoin trading scam. It was unknown to me that there were systematic ways to retrieve scammed funds.
I came across a business website who promised a huge return on investment. I was so convinced. The website was good and after all the convincing, I ended up depositing 150,000 USD, unfortunately, I fell into the wrong hands.
I was really devastated until I sent an email to an expert who came highly recommended – hackerone975 AT gmil co m
I gave him all the information about the events, and within a few working days, they restored 95% of my BTC back to my wallet. I was shocked and glad at the same time. With trustworthy people like hackerone975 , I can 100% guarantee your money will be recovered back
I was able to keep tabs on my partner with their spy apps They also helped me retrieve the funds that was stolen from me few months back.
contact them for help ;
spyhackelite at gmil co m
Everybody claiming they got helped by this and that hack specialist tried almost all non was legit , thank God i am done searching and got what i want i am leaving the internet. use no one else but bohdanbohdan93 @ mail . ru who is officially my plug.. if you need legit result hire him yourself please
A sense of uneasiness crept over me, indicating that something had occurred, and I could only hope for a favorable outcome. The drive back home felt like an eternity, the longest I had ever endured. However, upon reaching home, he was nowhere to be found. Another call to him went unanswered. Assuming he might still be at penelope’s residence, I contacted him, only to discover that he had left after their argument the previous night and she had not seen him since. In my quest for answers, I turned to the internet, where I came across hackerone975 at gmil do t com , who granted me access to my partner’s phone records. It was a smooth process and completely unnoticed from him.
It’s often said that intuition is a powerful tool, and in my case, it turned out to be true. I started noticing some red flags that hinted at possible infidelity. Late nights spent on the phone, secretive text messages, and a sudden need for privacy all raised my suspicions. These signs couldn’t be ignored any longer, and I knew I had to gather evidence to confront my partner. The mere thought of a cheating partner can evoke a whirlwind of emotions – anger, sadness, confusion, and even self-doubt. The suspicion alone can consume one’s thoughts, impacting their mental and emotional well-being. It was crucial for me to uncover the truth, not only for the sake of my relationship but also for my own peace of mind and CyberPunk Programmers offered a glimmer of hope, a chance to expose the truth and bring closure to a painful situation. While CyberPunk Programmers offers a promising solution, it’s important to understand both its benefits and limitations. On one hand, the service can shed light on a partner’s actions and provide concrete evidence. This was how I got to discover that I had no wife but only someone who just wanted to rip me off. Because of the comps, I now know where I stand and you too can know if you email them through cyberpunk (@) programmer (.) net
Analytics benchmark provides sql training in hyderbad The Tools sql Training hyderabad help Candidates to implement various data platform technologies into solutions that are in line with business and technical needs together with on-premises, cloud, and hybrid data scenarios integrating both relational and No-SQL data. Candidates will also get trained on how to process data using a range of technologies and languages for each streaming and batch data.
The rate at which people are scammed on the internet grows each day that passes, I was made to invest with a Binary option I saw online known MESIROFIN. At first I was able to withdraw the little investment and bonuses made, as time went I was required to invest more funds by the site manager which I did with promises grand bonuses . I invested $90,000 more with the site but everything came to a standstill when I wanted to withdraw my funds into my account but couldn’t, I contacted their support group with complaints but no help came forth. I was shell shocked when the site broke down the upper week after I had invest heavily with my funds, it was really a hard time going forward with the family because no more funds to exercise my financial wants and needs. Life was already devastating at that point and I didn’t know what to do or how to go about the predicament I was in, I really never lost hope on recovering my funds that I invested with the wrong platform. A friend I told my story recommended me to this particular recovery firm which brought my hopes alive. DARKRECOVERYHACKS with their team of formidable hackers restored my lost funds back swiftly within 72hrs and am really ever grateful to their SUPER RECOVERY FIRM for their services.
Modern relationships often involve a significant online presence. If you notice your partner spending excessive time on social media, engaging in secretive online conversations, or suddenly clearing their browsing history, it could be cause for concern. A sudden decline in emotional intimacy and changes in communication patterns can also be signs of infidelity. If your once open and communicative partner has become distant or avoids discussing certain topics, it may be worth exploring what lies bbeneath the surface. With cyberpunk, ( reach them through mail cyberpunk (@) programmer (.) net),you can keep tabs on incoming and outgoing calls, as well as text messages. This feature allows you to review conversations and identify any suspicious or out-of-character exchanges. Tell them I sent you.
It’s advisable for everyone to have an hacker buddy, an old friend nearly ruined my life when we fell out, but I was a step ahead when i got a hacker to hack into his phone. It was done in a couple hours and I had access to all his Text messages, WhatsApp, IG and Telegram messages. If you need help, reach out to Viktor via EMAIL: viktorhackworld @ gmail. com
He also helped my girlfriend fix her credit report after taking down late payments and other derogatory reports. To be honest, I never imagined anyone was capable of all these.
I would like to introduce you guys to this proficient hacker, although I have been used many times on this platform by fake hackers who turned out to be what they are not but he turned out different. I was almost giving up but thanks to Hackerone975 ,I contacted him VIA ” hackerone975 @ gm ail c o m” and he is very efficient, fast and reliable.
Honestly, The best thing that ever happened to me literally, was finding the contact of this genius Vadimwebhack@ gmail’com. This man granted me full access to an iPhone belonging to my girlfriend of 6 years. I saw her WhatsApp messages she was sending adult picture and videos to my so called friend and sleeping with him while I was away in Germany working so hard so we would have a better life. This genius helped me retrieve messages she deleted, emails and even call logs. she was doing this to me. I was away for just 6 months and was going to ask her to marry me when I got back Miami. I’m glad I followed my heart and again big thanks to Vadimwebhack@ gmail’com for not letting me ruin my own life. He recently helped a friend of mine fix his records, taking out hard inquiries and collections. He offers many other services I can’t mention here.
CyberPunk successfully gave me access to see alot going on inside my wife’s phone as I have seen that she has other guys she is meeting at hotels. My happiest feeling now is that she is not even aware yet about this because CyberPunk were very good that she has no idea that I have tapped into her phone.
Email cyberpunk@programmer.net
Get into your spouses and kids phones and other gadgets without them knowing or suspecting. It feels good and safe to know what your family members and loved one’s does at always without them knowing . I had always thought it was never possible to monitor your partner or children without them noticing, but all thanks to him I am able to view my partners activities without her even knowing
Write to :
urbanghosthacker at gm ail co m
Let’s be real – sometimes we need a little expert advice to navigate the treacherous academic waters. Daniel Meuli Web Recovery understands this and provides you with access to knowledgeable mentors and a treasure trove of educational resources. Whether you need help with specific concepts, guidance on effective study techniques, or simply a pep talk to boost your motivation, Daniel Meuli Web Recovery has got your back. Consider it your own personal support system, helping you regain your grade with a touch of magical expertise. Once you know where to focus, it’s time to devise a strategy for success. Daniel Meuli Web Recovery takes the guesswork out of planning by creating personalized study plans tailored to your needs. These study plans are like roadmaps to academic triumph, guiding you through the necessary steps, resources, and timelines to regain your grade. It’s like having your GPS, but instead of “recalculating,” it says “recalibrating your path to success. To embark on your academic recovery journey with Daniel Meuli Web Recovery, the first step is to create an account and set up your profile. It’s like enrolling in a magical academy but without the pesky owls and flying broomsticks. Follow the intuitive sign-up process, provide some basic information, and voila! You’re ready to dive into the world of academic rejuvenation. Email Daniel Meuli web recovery on DANIELMEULIWEBRECOVERY (@) EMAIL. COM OR TELEGRAM (@) DANIELMEULI
I’m pleased with Spyweb Cyber Security Service for the recovery of my stolen crypto funds. A few months ago, I was duped by a fake crypto investment broker of my hard-earned money. I had invested $409,000 worth of Bitcoins and ETHEREUM into this platform and I was blocked from withdrawing my profits. A colleague of mine told me about Spyweb Cyber Security Service and their experience in the recovery process, I did my research and found Spyweb Cyber Security to be a genuine and reliable recovery service, I contacted them immediately and provided them all the necessary information. I was very impressed when they were able to recover my stolen crypto funds from these broker accounts. I’m truly grateful for their service and I feel it is right that I put this out here for anyone who might require their services. Spyweb Cyber Security Service is very reliable and trustworthy. You can contact them directly at ( Spyweb@Cyberdude.com )
WEBSITE: ( https://spyweb3.wixsite.com/spywebcyber )
WHATS-APP: ( +1 720 625 0393 )
I Carefully read a review about Hackerone975 at gmil c0m that has been endorsed by several people, therefore I am not the first to do so, but I still want to express my happiness at having made the right decision in trusting my gut and Hackerone975 at Gmil C0m positive evaluations. I would have still been deeply in debt if not for the decision I made, but Hackerone975 has now eliminated all of that debt. Everyone, including you, is entitled to be delighted, thus in order to obtain it, I advise you to get in touch with the top players. Anyone who has suffered a loss in cryptocurrency trading can get help from Hackerone975 at gmi,l com trust your mind for that.
Whether you’re looking for personal or business-related service, hiring a professional hacker from dark web firm thehackerspro.c0m guarantees complete privacy while offering top-notch quality service although they can be somewhat pricey.
So if you’re in need of any type of hacking solution look no further than open a fast case with Vladimir kolarov on telegram with @h4ckerspro
It’s better way off to see what has been hidden from someone in a relationship, no one would want if he or she is been cheated on, for this reason taking a few extra steps in getting what would serve as a proof for leaving a toxic relationship isn’t a bad idea, yes that’s me justifying myself. This is because sometimes ago I was searching for an app that would serve me the purpose of monitoring and spying on my spouse’s phone, unfortunately the apps I laid my hands on wasn’t giving me much of what I needed, but a review about a person who could help me out changed the scenario. After I read that I could send a mail to techspypro @gmail com, where I could use the help of an expert who will help in getting me information and track my spouse’s real-time location, I did in a good faith and fortunately it was what I wanted, I had to explain how I want to see all information that has been deleted, access to the real time location and calls from my spouse’s phone, it was within hours when I got a mail back from the expert, giving me access links and how to make use of them in getting all I requested. I decided to share this because information is power, if I had not read someone’s review about the way out, I could have been in the dark for God knows when, but I’m glad that’s not the case.
Life can be so cruel sometimes but even worst when you have a cheating partner. I got to discover my spouse was having an affair through the help of { hackerone975 @ gm ail c o m } who gave me access to his device remotely without his notice. I got access to all social media apps, call logs and sms and deleted datas and messages too. Do not be a victim to lies and mischief. Get in contact with him and stay safe.
In this day and age of advanced technology, social media, and the “jet age,” people frequently have to deal with legitimate and fraudulent opportunities that are presented to them online. It is inevitable that people will come across fraudulent websites and imposters who are trying to defraud people of their hard-earned money or assets in any way possible. I was one of the victims of this story, having lost a total of $587,132 to a con artist posing as a procurement agent on a website for procurement.
I was left bewildered and heartbroken, unable to comprehend my circumstances or how to get my money back. However, I am grateful to Kingston Technologies for helping me solve my problem as I contacted him when I read a review of his services. If you ever experience anything similar to what I did, or if you have any questions about online fraud, you should definitely use his services. You can reach him directly at kingston@cyber-wizard.com
I am grateful for the miraculous recovery Morrison’s expertise brought into my life.
I fell victim to an internet scammer who took advantage of my trust and stole my hard-earned investment money. I was devastated and felt hopeless. However, thanks to Morrison’s recovery services, I was able to recover every cent that was taken from me. Their professionalism and dedication to helping people in need truly saved me from financial ruin. I am forever grateful for their assistance and would highly recommend them to anyone facing a similar situation. Thank you, Morrison@cyber-wizard.com, for restoring my faith and securing my future.
Thank you, Morrison’s recovery, for your exceptional assistance.
“I am thrilled to share how Morrison’s recovery services were a true blessing in helping me recover my lost Bitcoin investments from an internet scammer. Their professionalism, dedication, and expertise made the entire process streamlined and stress-free. Thanks to their prompt action and relentless pursuit of justice, I was able to retrieve the funds that I had thought were lost forever. I highly recommend Morrison’s recovery services to anyone who finds themselves in a similar situation. Thank you, Morrison@cyber-wizard.com team, for your invaluable assistance!”
Investigating infidelity in my relationship led me to Crypto Pandemic Hunter, a digital agency with advanced tools to uncover secrets. Their discreet methods allowed me to track my partner’s digital activities, revealing his multiple affairs. Confronted with undeniable evidence, I experienced a mix of emotions but also found empowerment in knowing the truth. Thanks to the professionalism and empathy of Crypto Pandemic Hunter, I was able to make informed decisions and move forward from betrayal. I highly recommend their services to anyone facing similar doubts about their partner’s faithfulness. For assistance with uncovering the truth, contact cryptopandemichunter [@] consultant. com.
I finally ended it after the most clear evidence I’ve gotten. I’ve been suspicious of her for 8 months as she slowly stopped showing me affection and wouldn’t even hold my hand when walking around stores like we used to do, when I first asked her why her tattoo artist was calling her during dinner (around 8:15-8:30pm) and she quickly denied it and set her phone to silent mode, she stammered a bit and said that he probably just wanted to check up on how her recent tattoo she had gotten was healing. I didn’t buy any of that and decided to hire this hacker to help get me access to all of her device [ CoolKiid (a) Pro ton * Me ], found out she was cheating, I read through all the inappropriate text messages and pictures they shared.Contact this hacker if you are in a similar situation and looking for answers.
I appreciate Techspymax for making me realise the truth to a certified hacker who knows a lot about what his doing. I strongly recommend you hire him because his the best out there and always delivers. I have referred over 10 people to him and all had positive results. He can help you hack into any devices, social networks including – Facebook, Hangout, iMessages, Twitter accounts, Snap chat , Instagram, Whatsapp, wechat, text messages ,smartphones cloning ,tracking emails and also any other social media messenger or sites. It’s advisable to hire a professional hacker. Thank me later. Contact him here.techspymax @ gm ail c o m